Understanding asymmetric encryption: The key to safer digital communication
Secure online communication requires a way for two parties to exchange information privately, even if they've never interacted before. Asymmetric encryption makes this possible and has become a foundational part of modern digital security.
This article explains what asymmetric encryption is and how it works, including key pairs and the algorithms behind them. It also explores the real-world applications, tradeoffs, and its role in both current and emerging security models.
What is asymmetric encryption?
Asymmetric encryption, also called public-key encryption, is a method of protecting data using two mathematically linked cryptographic keys: one public, one private. It's called "asymmetric" because it uses two different keys rather than one shared key. This sets it apart from other forms of data encryption that rely on a single secret key.
Asymmetric encryption vs. symmetric encryption
Both asymmetric and symmetric encryption use cryptographic keys to protect data, but they differ in a fundamental way.
Symmetric encryption uses a single shared key for both encryption and decryption. This makes it fast and well-suited for encrypting large volumes of data, like database contents or ongoing network traffic. But it creates a challenge: both parties must somehow share that secret key securely.
Asymmetric encryption addresses this problem by using two separate keys: a public key and a private key. The public key can be shared openly without revealing the private key, so the parties don't need to pre-share a secret key in advance. In practice, the two approaches often work together: public-key cryptography is used to authenticate parties or establish a shared secret, and symmetric encryption then handles the bulk data transfer.
Why asymmetric encryption matters
Before public-key cryptography, secure communication over open networks depended on pre-shared secrets or other key-distribution methods, which were difficult to scale. This made secure communication between previously unconnected parties far less practical.
Asymmetric encryption changed that. Allowing anyone to publish a public key made it much easier for two parties with no prior relationship to begin communicating securely.
This shift didn't just improve security; it helped make the architecture of the modern internet viable. Online commerce, remote system access, software signing and distribution, and secure messaging all rely on this foundational capability.
Read more: Encryption protocols explained: What they are and how they work.
How does asymmetric encryption work?
Asymmetric encryption relies on three core processes: generating key pairs, encrypting and decrypting data, and creating digital signatures.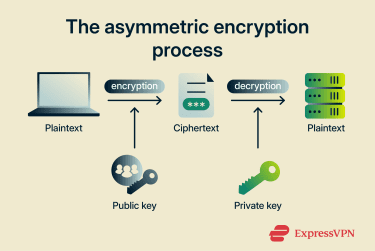
How key pairs are generated
Key generation creates two related keys: a private key and a corresponding public key. The exact process depends on the algorithm. For example, Rivest–Shamir–Adleman (RSA) key generation uses large prime numbers, while elliptic-curve systems generate a private key and derive the public key through elliptic-curve operations.
The two keys are mathematically related, but knowing the public key does not make it practical to determine the private key. This is what makes it safe to share the public key openly.
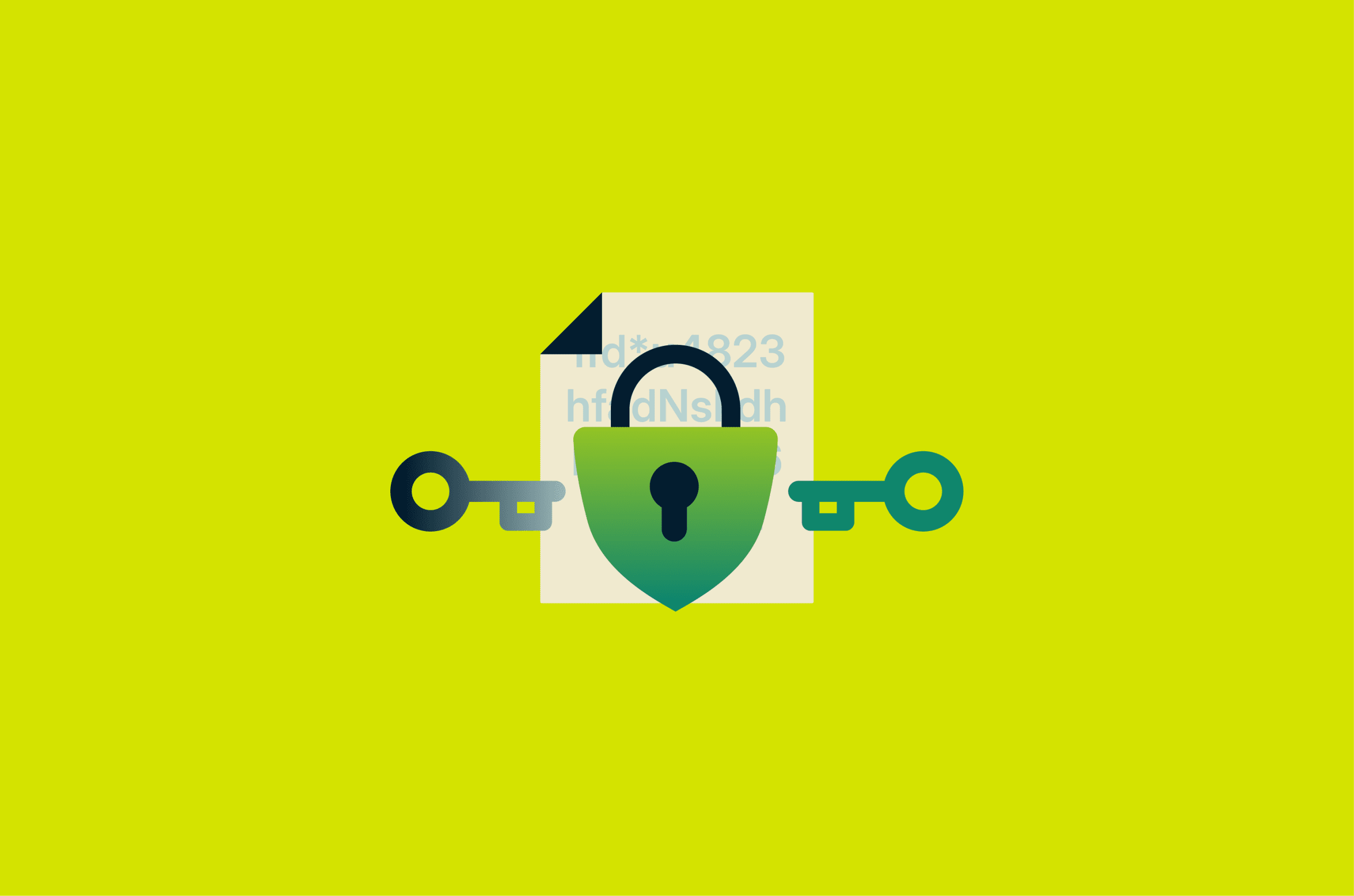
How encryption and decryption happen
When someone sends a private message, the system passes the unencrypted content (plaintext) through an encryption algorithm along with the recipient's public key. The algorithm performs a series of mathematical operations on these inputs, producing an unreadable output known as ciphertext.
At the other end, the recipient’s private key is used in the corresponding decryption process. Because of the mathematical relationship between the two keys, the private key allows the original message to be recovered.
How digital signatures prove authenticity
A digital signature is a piece of data attached to a message or document that helps verify who signed it and whether it has been changed since. Instead of protecting confidentiality, it's used to support authenticity and integrity. While encryption uses the recipient's public key to protect data, a signature uses the sender's private key to generate a value that the sender's public key can verify.
The process usually starts by running the original data through a hashing algorithm, which produces a fixed-length digest often described as a fingerprint of the content. Even a small change to the input produces a different hash. The sender’s private key then generates a signature based on this hash.
When the recipient receives the data and signature, verification uses the sender’s public key, the signature, and the received data. The received data is hashed again, and the signature algorithm checks whether the signature is valid for that hash and public key. If so, the signature is considered valid. If not, it's rejected.
Common asymmetric encryption algorithms
As covered earlier, asymmetric encryption relies on mathematical problems that are easy to compute in one direction but practically impossible to reverse. Each algorithm applies this principle to a different type of problem.
Rivest-Shamir-Adleman
The RSA algorithm is built on the integer factorization problem: the difficulty of factoring large numbers. Multiplying two large primes together is simple, but working backward from the result to find those original primes is not.
To create a key pair, RSA generates two large prime numbers and multiplies them. The result becomes a shared component used in both keys. The public key pairs this value with an exponent, while the private key uses related values to reverse the process or generate signatures.
RSA's strength depends on the size of those original primes. In practice, they're hundreds of digits long, producing keys of at least 2048 bits, with 4096-bit keys used for higher security. The tradeoff is that working with values this large requires more processing power, making RSA slower than some alternatives.
Elliptic Curve Cryptography
Elliptic Curve Cryptography (ECC) serves many of the same broad purposes as RSA, especially digital signatures and key exchange, but achieves comparable security with much smaller keys.
It relies on the elliptic curve discrete logarithm problem. Key generation starts with a random number (the private key), which is used to calculate a point on a predefined mathematical curve through repeated point addition. The resulting point becomes the public key. There's no feasible way to determine the private key from the public key.
Because smaller keys provide equivalent strength, ECC is often more efficient than RSA for operations like signing messages, verifying identities, and establishing shared secrets.
Diffie-Hellman key exchange
Diffie-Hellman (DH) doesn't encrypt data directly. Instead, it lets two parties agree on a shared secret key, which is then used by a symmetric encryption algorithm to protect the actual data. For example, DH combined with ECC, known as Elliptic-curve Diffie–Hellman (ECDH), is used to secure modern Wi-Fi connections.
The exchange starts with both parties agreeing on shared public parameters. Each party then independently picks a private value and uses the shared parameters to compute a public value, which they exchange openly. Each side combines the other's public value with its own private value, and both arrive at the same shared secret, without that secret ever crossing the network.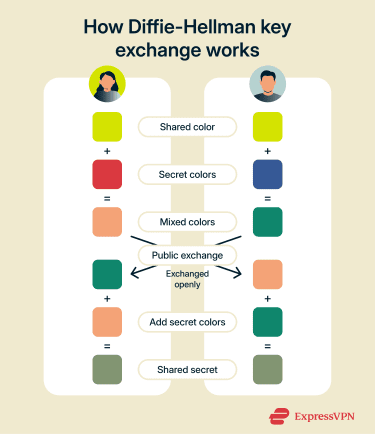
Here’s a brief comparison of the most common asymmetric encryption algorithms:
| Algorithm | Primary use | Key size | Speed |
| RSA | Signatures, encryption, and key transport | Large (2048+ bits) | Slower |
| ECC | Key exchange and signatures | Small (for example, 256 bits) | Often faster |
| DH | Key exchange only | Varies | Varies |
Other common algorithms
While RSA, ECC, and DH are the most widely used, a few other asymmetric algorithms fill more specialized roles.
The Digital Signature Algorithm (DSA) is designed specifically for creating and verifying digital signatures; it doesn't handle encryption or key exchange. It's defined by the National Institute of Standards and Technology (NIST) Digital Signature Standard (DSS), but it's now mainly a legacy algorithm rather than a common choice for new systems.
ElGamal supports both encryption and digital signatures and is closely related to DH in its underlying math. It's less common in everyday web security but appears in tools like GNU Privacy Guard (GnuPG) for secure messaging and in certain privacy-focused cryptographic schemes.
Real-world applications of asymmetric encryption
Many everyday technologies rely on asymmetric encryption. A few common examples include:
- HTTPS and Transport Layer Security (TLS): HTTPS connections use TLS to protect communication between browsers and servers. During the TLS handshake, asymmetric encryption helps verify the server's identity and establishes the session keys used to encrypt the connection. This protects data in transit, such as logins, financial transactions, and other sensitive web traffic, from interception and man-in-the-middle (MITM) attacks.
- Secure email and messaging: Protocols like Secure/Multipurpose Internet Mail Extensions (S/MIME) and Pretty Good Privacy (PGP) use asymmetric encryption to protect email so that only the intended recipient can decrypt it, even as messages pass through multiple servers. Messaging apps like WhatsApp or Signal rely on similar principles: using asymmetric key agreement to establish end-to-end encrypted conversations.
- Digital signatures and authentication: In practice, digital signatures support identity verification in scenarios like passwordless logins, remote Secure Shell (SSH) connections, and software distribution. They also help show whether signed contracts or transactions have been altered and can support non-repudiation when the signer’s identity is reliably tied to the signing key.
- Digital certificates and public key infrastructure (PKI): Websites use digital certificates to prove their identity to browsers. Behind the scenes, certificate authorities (CAs) validate control of a domain and sign these certificates using asymmetric encryption. Browsers then verify those signatures and warn or block access when a certificate is missing, expired, or invalid.
Advantages and limitations of asymmetric encryption
Asymmetric encryption improves security, but it also comes with performance and scalability constraints.
Key benefits of asymmetric encryption
The main benefits of asymmetric encryption apply to key exchange and signatures:
- No shared secret required: Public keys are designed to be shared openly, so two parties can establish secure communication without first exchanging a secret key through a private channel. This is the core advantage over symmetric encryption and what makes secure communication across open networks practical.
- Trust without prior relationships: Digital signatures help systems verify integrity and authenticate a signer when the corresponding public key is trusted. This scales through mechanisms such as CAs, PKI, and electronic signature systems used to verify identities, transactions, and signed documents.
- Confidentiality by design: Because only the corresponding private key can decrypt what the public key encrypts, properly implemented public-key encryption helps keep data private even if it's intercepted in transit.
Common limitations and trade-offs
The most noteworthy limitations of asymmetric encryption arise when dealing with large volumes of data:
- Computational cost: The mathematical operations underlying asymmetric encryption are significantly more resource-intensive than those of symmetric encryption. This is why asymmetric encryption is typically used only for key establishment, authentication, and signatures, not for encrypting bulk data.
- Data size constraints: Some algorithms, like RSA, can only process inputs smaller than their key size in a single operation. This makes asymmetric encryption impractical for large files or continuous data streams on its own; it's almost always paired with symmetric encryption for that purpose.
- Key management complexity: While it eliminates the need to share secrets in advance, asymmetric encryption introduces its own overhead: generating and storing key pairs, maintaining certificate trust chains via CAs and PKI, and handling key and certificate expiration and revocation. Misconfiguration at any point can undermine the entire system.
These tradeoffs are why asymmetric encryption is rarely used on its own. In practice, most systems use a hybrid approach: public-key cryptography handles authentication and key establishment, then symmetric encryption takes over for the bulk data transfer. Each method addresses the other’s weakness: asymmetric encryption solves the key distribution problem, and symmetric encryption provides the speed needed for ongoing communication.
Is asymmetric encryption safe for modern security?
When properly implemented with well-established algorithms and recommended key sizes, asymmetric encryption remains secure against current classical threats.
Brute-forcing an asymmetric key is computationally infeasible, as the number of possible combinations far exceeds what modern hardware can process in any practical timeframe. Known attacks that are more efficient than brute-force exist for specific algorithms, but they're still not fast enough to break keys of currently recommended sizes.
The more significant long-term concern is quantum computing. Shor's algorithm, if run on a sufficiently powerful quantum computer, could solve the mathematical problems underlying RSA, ECC, and DH far faster than classical computers. How soon that becomes practical is still uncertain, but the cryptographic community isn't waiting to find out.
In 2024, NIST published its first set of post-quantum encryption standards, including the Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM) and the Module-Lattice-Based Digital Signature Algorithm (ML-DSA).
These algorithms are built on lattice-based mathematics: problems involving complex, multi-dimensional structures that remain difficult to solve even for quantum computers. A third standard, Stateless Hash-Based Digital Signature Algorithm (SLH-DSA), uses hash-based signatures as an alternative approach. Together, these standards mark the beginning of the transition to post-quantum cryptography.
FAQ: Common questions about the asymmetric encryption
Why is asymmetric encryption slower than symmetric encryption?
How do public and private keys work together?
What is the difference between encryption and digital signatures?
Can asymmetric encryption protect data in transit?
How is asymmetric encryption used in HTTPS?
What happens if a private key is exposed?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN