-
What is network jitter, and how does it impact internet performance?
Network jitter, or packet delay variation, happens when data packets experience inconsistent delivery times due to congestion or routing changes. This inconsistency directly affects real-time applicat...
-

Desktop virtualization: The complete guide
Most of us might think of a desktop as something fixed to a single machine. But what if your desktop wasn’t tied to the hardware at all? With desktop virtualization, your entire environment can run ...
-
Internet infrastructure: What it is and how it works
The internet feels so simple: you tap a screen, click a mouse, and enjoy a whole world of information and connections, right there at your fingertips. Behind the scenes, however, the internet is anyth...
-
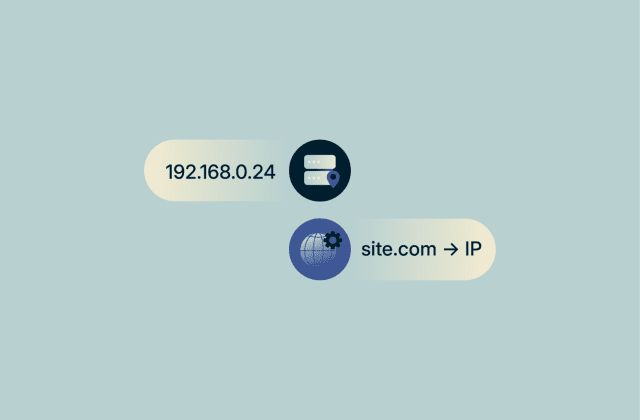
DHCP vs. DNS: Understanding key differences and functions
Every time a device goes online, it relies on two background services. One gives your device the settings it needs to join a network, and the other turns domain names like “example.com” into the n...
-

What is OpenVPN, and how does it work?
OpenVPN is one of the most widely used and trusted VPN protocols in the industry. It has a strong reputation built on its robust encryption and proven security design, as well as its open-source code....
-

What are data brokers? A complete guide to your privacy and protection
Every time you browse the web, sign up for a service, or fill out an online form, traces of your personal life are being collected. Sometimes, this information is collected and sold by companies known...
-
How to remove yourself from data broker sites and protect your privacy
Data brokers make their money by collecting personal information about consumers and reselling it. That information can be funneled into public people search sites, sold to advertisers, shared with in...
-
Fast flux networks: Complete guide to risks and detection
Fast flux is a Domain Name System (DNS)-based evasion technique that rapidly rotates the IP addresses associated with a malicious domain so that it doesn’t remain at a single host. Attackers achieve...
-
How to protect your email: Step-by-step guide
Your email account is an important point of access to the rest of your online life. Many services use it as the primary recovery channel, so whoever controls your inbox can request password resets, in...
-
Split tunneling vs. full tunneling: Which should you use?
A virtual private network (VPN) can be configured to handle your traffic in two modes: full tunneling and split tunneling. With full tunneling, all your traffic goes through the VPN, whereas with spli...

Don't miss the Spring Deal: Save up to 78% before April 21.
Don't miss the Spring Deal: Save up to 78% before April 21. Claim now!
Claim Now!

